Research study reveals evident Iranian state hackers attempting to pirate consumer-grade cams.
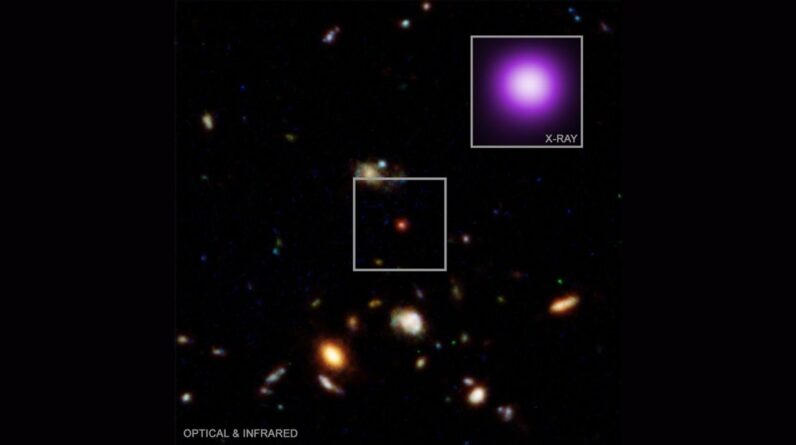
Electronic cameras are positioned in public locations in Tehran.
Credit: Anadolu/Getty Images
For years, satellites, drones, and human spotters have actually all belonged to war’s monitoring and reconnaissance tool set. In an age of low-cost, insecure, Internet-connected customer gadgets, nevertheless, armed forces have actually gotten another effective set of eyes on the ground: every hackable security video camera set up outside a home or on a city street, pointed at prospective battle targets.
On Wednesday, Tel Aviv– based security company Check Point launched brand-new research study explaining numerous hacking efforts that targeted consumer-grade security cams around the Middle East– with lots of obviously timed to Iran’s current rocket and drone strikes on targets that consisted of Israel, Qatar, and Cyprus. Those camera-hijacking efforts, a few of which Check Point has actually credited to a hacker group that’s been formerly connected to Iranian intelligence, recommend that Iran’s armed force has actually attempted to utilize civilian monitoring cams as a way to identify targets, strategy strikes, or examine damage from its attacks as it strikes back for the United States and Israeli battles that have actually triggered an expanding war in the area.
Iran would not be the very first to embrace that camera-hacking monitoring technique. Previously today, the Financial Times reported that the Israeli armed force had actually accessed “almost all” the traffic video cameras in Iran’s capital of Tehran and, in collaboration with the CIA, utilized them to target the air campaign that eliminated Ayatollah Ali Khamenei, Iran’s supreme leader. In Ukraine, the nation’s authorities have actually cautioned for several years that Russia has actually hacked customer monitoring electronic cameras to target strikes and spy on troop motions– while Ukrainian hackers have actually pirated Russian cams to surveil Russian soldiers and maybe even to monitor its own attacks.
Making use of the insecurity of networked civilian electronic cameras is, to put it simply, entering into the standard procedure of militaries worldwide: A fairly low-cost and available ways of getting eyes on a target numerous countless miles away. “Now hacking cams has actually entered into the playbook of military activity,” states Sergey Shykevich, who leads danger intelligence research study at Check Point. “You get direct presence without utilizing any pricey military ways such as satellites, frequently with much better resolution.”
“For any assailant who is preparing military activity, it’s now a simple act to attempt it,” Shykevich includes, “since it’s simple and offers great worth for your effort.”
In the current example of that reconnaissance strategy, Check Point discovered that hackers had actually tried to make use of 5 unique vulnerabilities in Hikvision and Dahua security cams that would have permitted their takeover. Shykevich explains lots of efforts– which Check Point states it obstructed– throughout Bahrain, Cyprus, Kuwait, Lebanon, Qatar, and the United Arab Emirates, along with hundreds more in Israel itself. Inspect Point notes it might see attempted invasions just on networks geared up with its firewall software network home appliances which its findings are most likely altered by the business’s fairly bigger consumer base in Israel.
None of the 5 vulnerabilities are “complex or advanced,” Shykevich states. All of them have actually been covered in previous software application updates from Hikvision and Dahua and were found years earlier– one as early as 2017. As with hackable bugs in so lots of Internet-of-things gadgets, they continue in security video cameras since owners hardly ever set up updates or even end up being mindful that they’re readily available. (Hikvision and Dahua are both successfully prohibited in the United States due to security issues; neither business reacted to WIRED’s ask for talk about the hacking project.)
Inspect Point discovered that the camera-hacking efforts were mostly timed to February 28 and March 1, simply as the United States and Israel were starting their air strikes throughout Iran. A few of the tried video camera takeovers likewise took place in mid-January, as demonstrations spread out throughout Iran and the United States and Israel made preparations for their attacks. Inspect Point states it has actually connected the targeting of the video cameras to 3 unique groups it thinks to be Iranian in origin, based upon the servers and VPNs they utilized to perform the project. A few of those servers, Shykevich notes, have actually been formerly connected in specific to the Iranian hacker group called Handala, which numerous cybersecurity business have actually determined as dealing with behalf of Iran’s Ministry of Intelligence and Security.
Inspect Point states it tracked comparable Iranian targeting of cams as early as last June throughout Israel’s previous 12-day war with Iran. The head of Israel’s National Cybersecurity Directorate, Yossi Karadi, likewise cautioned at the time that Iranian hackers were utilizing civilian electronic camera systems to target Israelis and had actually jeopardized a street video camera throughout from the nation’s Weizmann Institute of Science before striking it with a rocket.
The joint United States and Israeli strikes on Iran and the assassination of Khamenei have actually exposed, nevertheless, simply how completely Israel’s own hackers– or those of its allies, consisting of possibly the United States– had actually permeated Tehran’s video camera systems, too. Israeli intelligence sources speaking with the Financial Times explained putting together the patterns of life of Iranian guard around Khamenei based upon the real-time information that traffic electronic cameras offered throughout the city. “We understood Tehran like we understand Jerusalem,” one source informed the FT.
Prior to the present intensifying war in the Middle East, the effective monitoring function of hacked civilian cams initially emerged in the middle of Russia’s war in Ukraine. Ukrainian authorities cautioned in January 2024, for example, that Russian forces had actually hacked 2 security video cameras in the capital of Kyiv to observe Ukrainian facilities targets and air defenses. “The assailant utilized these cams to gather information to prepare and change strikes on Kyiv,” checks out a post from Ukraine’s SSU intelligence service.
The SSU presumed, it composes, regarding in some way disable 10,000 Internet-connected electronic cameras– it didn’t expose how– that might be utilized by Russia’s military. “The SSU is contacting the owners of street web cams to stop online broadcasts from their gadgets, and on residents to report any streams from such cams,” the post checks out.
Even as Ukraine has actually tried to obstruct that spying method, it appears likewise to have actually embraced it. When the Ukrainian military utilized its own undersea drone to explode a Russian submarine in the bay of Sevastopol in Crimea, it released video that defense-focused news outlet The Military Times kept in mind looked quite like it had actually originated from a hacked monitoring video camera. A BBC report about Ukrainian hacktivist group One Fist notes more clearly that they were applauded by the Ukrainian federal government for work that consisted of hacking video cameras to view Russia’s motion of matériel throughout the Kerch Bridge in between Russia and Crimea.
“The benefits of co-opting a civilian video camera network are existence and cost,” states Peter W. Singer, a military-focused scientist at the New America Foundation and the author of the 2015 sci-fi unique Ghost Fleetwhich pictures future war situations. “The foe’s currently done the work for you. They’ve positioned cams all around a city.”
Vocalist keeps in mind that hacking those cams is greatly less expensive and simpler than depending on satellites or high-altitude drones. The technique is stealthier than drones, too, which are just feasible when the opponent has couple of air defenses, and drones can frequently be discovered by countersurveillance procedures. Ground-level, hacked video cameras likewise use angles and viewpoints that aren’t possible with the bird’s-eye view of a satellite or drone, he includes. All of that makes them effective tools for reconnaissance, targeting, and what he calls “bomb damage control” after a strike.
Hacked video cameras are a hard issue to resolve, in part, since those who have the capability to protect them hardly ever suffer the repercussions of that monitoring, states Beau Woods, a security scientist who previously worked as an advisor to the United States Cybersecurity and Infrastructure Security Agency. “The producer of the gadget and the owner of the gadget are not the victim,” Woods states. “So the victim isn’t in a position to manage the tool that’s utilized by the foe.”
The trouble of determining duty for Internet-connected customer electronic cameras indicates that their function in military security is most likely to continue for several years– and wars– to come.
“Who’s accountable, who’s accountable, who’s liable?” Woods asks. “The cam itself is not straight triggering the damage. It’s part of the kill chain.”
This story initially appeared on wired.com.
Wired.com is your necessary everyday guide to what’s next, providing the most initial and total take you’ll discover anywhere on development’s influence on innovation, science, company and culture.
82 Comments
Find out more
As an Amazon Associate I earn from qualifying purchases.