A strategy that hostile nation-states and economically inspired ransomware groups are utilizing to conceal their operations postures a danger to vital facilities and nationwide security, the National Security Agency has actually alerted.
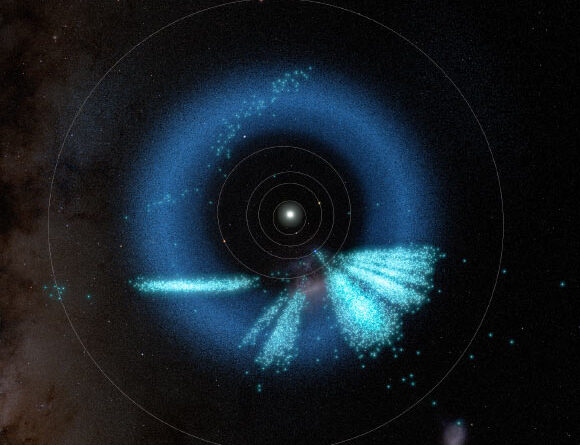
The method is called quick flux. It enables decentralized networks run by hazard stars to conceal their facilities and endure takedown efforts that would otherwise prosper. Quick flux works by biking through a series of IP addresses and domain that these botnets utilize to link to the Internet. Sometimes, IPs and domain alter every day or more; in other cases, they alter practically per hour. The consistent flux makes complex the job of separating the real origin of the facilities. It likewise offers redundancy. By the time protectors obstruct one address or domain, brand-new ones have actually currently been appointed.
A considerable danger
“This method presents a considerable risk to nationwide security, making it possible for destructive cyber stars to regularly avert detection,” the NSA, FBI, and their equivalents from Canada, Australia, and New Zealand alerted Thursday. “Malicious cyber stars, consisting of cybercriminals and nation-state stars, utilize quick flux to obfuscate the places of harmful servers by quickly altering Domain Name System (DNS) records. In addition, they can produce durable, extremely readily available command and control (C2) facilities, hiding their subsequent harmful operations.”
A crucial methods for accomplishing this is making use of Wildcard DNS records. These records specify zones within the Domain Name System, which map domains to IP addresses. The wildcards trigger DNS lookups for subdomains that do not exist, particularly by connecting MX (mail exchange) records utilized to designate mail servers. The outcome is the task of an opponent IP to a subdomain such as malicious.example.com, although it does not exist.
Learn more
As an Amazon Associate I earn from qualifying purchases.